I’m running a website that is getting a lot of bot traffic and found Cloudflare free rule tier to be a bit limiting. (5 custom rules with length limits)
Ive got subnets for major VPS providers to block and will run analysis against my traffic to build on these lists.
What do others do?
I’m contemplating my Cloudflared tunnel into Crowdsec to my app.
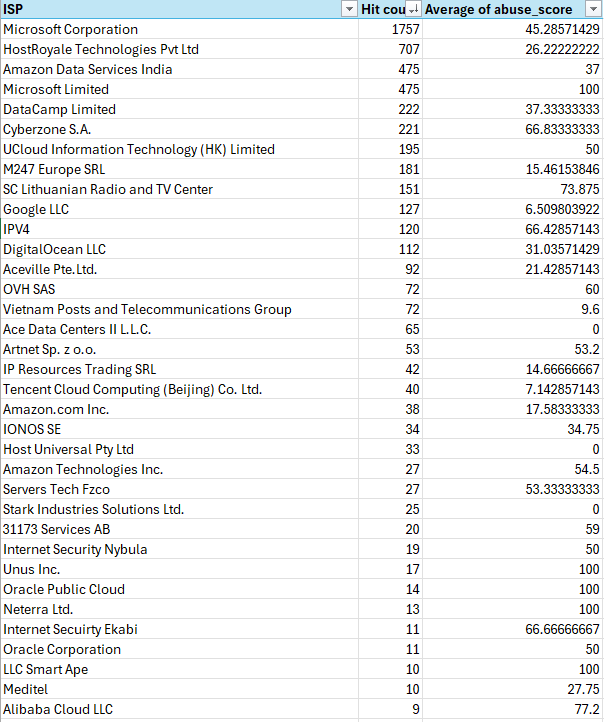
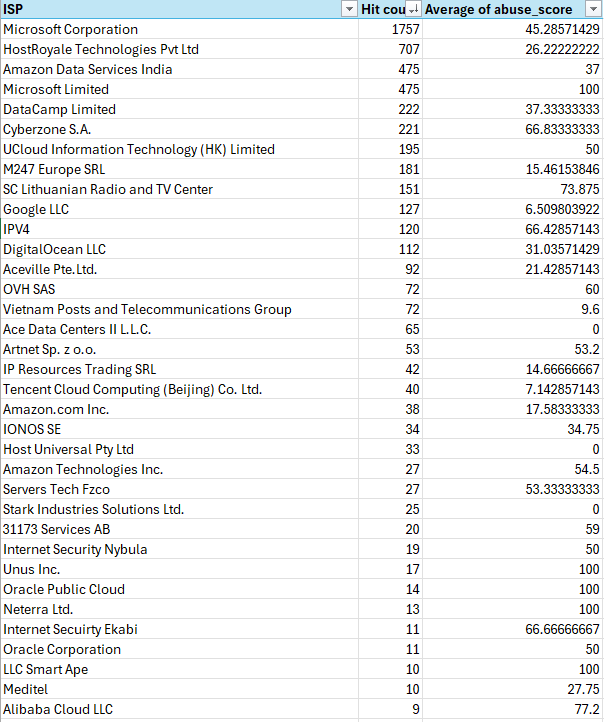
Edit: Adding in image of my analysis of the IPs scanning for vulnerabilities.
https://github.com/fail2ban/fail2ban
You can set
dbpurgeageto30dand pretty much just run it–or you can setupjail.confwith abantime.factor. Its appeal is that you basically can download it, enable it, and it just works for you. It depends on your environment, though. If you have incoming authorized requests from other services it might be a pain to configure, but I’ve never used anything easier to protect you from bad actors.Give openappsec a try. It’s not entirely Open Source, howerver you don’t need to share anything with the company behind it (Check Point), and the solution “Just works” most of the time (fail2ban support included) without the hassle of adjusting a multitude of rules thanks to the use of AI. Just install and forget about it. I only had to create one custom rule, so the WAF would allow the upload of big files into my Nextcloud server. Keep in mind I only expose a couple of my own services to the Internet, that only me and couple of friends of mine will use, so I doubt I can be very representative here.
Wafs don’t make you safer but create unnecessary attack surface. Just keep your machine and services up to date.
I’m trying to block the most likely attack vectors which is definitely VPS providers at this point in time. I just figure if I am blocking subnets plus additionals I identify it will force them out of these vectors to attack in ways I might be able to report better abuse.
Here check out my analysis.
Just don’t run broken software. The attackers will not be able to exploit you then. If they have zero day exploits, the WAF will most of the time not save you since they are often pretty easy to circumvent. WAFs are only effective against old and shitty exploits that should be patched anyways since ages.
I’d rather not have them probing my website at all. I’m not Facebook, my data is not unlimited and free.
Welcome to the internet. You will be probed. Just as your immune system, or rather your body, is being probed.


